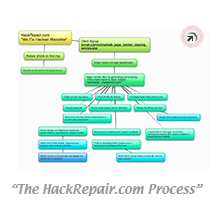
Personalized and Caring Involvement in Fixing Your Hacked Website– It’s What We Do.
Learn about our website security review service if you think your webmail may be compromised.
- Our goal is to help you prevent your website from being hacked again.
- Service is very important to us. We intend to reply to every email you send us within five minutes; and likewise begin working to fix your website within minutes of your call.
 No outsourcing to an unknown sweatshop of workers in some unknown country. We are a California-based business.
No outsourcing to an unknown sweatshop of workers in some unknown country. We are a California-based business.- We consider every phone call we receive a blessing. Call us anytime, (619) 479-6637, or Toll-Free, (800) 639-6442, or email, jim at hackrepair dot com
- Once we’ve completed the clearing of malware from your website we will, with your approval, help you install software to better secure your website in the future.
- Throughout the course of cleaning your hacked website, we will provide you with a real-time report on what we are doing, what we’ve found, and what to watch out for in the future.
- Even after your website has been secured and Google.com reputation restored we will remain available by phone or email for any questions you may have in the future. Think of us as “your website security experts for life!”
- With fifteen years of web hosting and Internet security-related experience, our skill sets are unique and available to you for a reasonable flat fee.
- We treat every hack repair project we work on as though it were our own website.
Our service goals include:
1. Education.
Our #1 goal is to ensure your website is never hacked again. We hope to impart to you all of the lessons we’ve learned from previous clients and help make you a WordPress security guru by the time we are finished.
2. Reporting.
Our #2 goal is to report back to you everything we’ve done, including showing you what malware looks like and how to locate it.
3. Long term security.
Once we’ve cleared all malware from your website, our goal #3 is to better secure your website from random bots and other malicious folk. Below are some of the tasks we intend to build into your website (for WordPress clients):
- Enable a 404 error detection. This helps to block random bots of finding you.
- Enable backups. We don’t want all of our good works lost due to accidental file deletion.
- Enable brute force login protection. This will help block hackers from attempting to guess your password.
- Enable file locking so hackers cannot edit core WordPress files.
- Enable real-time logging within your site. This will notify us if something changes within your site unexpectedly.
- Enable settings to reduce comment spam.
- Enable you to better secure your website by teaching you security best practices.
- Enable your website to deny the execution of scripts within image directories. This helps to discourage hackers from hiding back door scripts within directories you would not normally check or monitor.
- Enable real-time file monitoring.
- And much more…
Who is Jim Walker, The Hack Repair Guy?