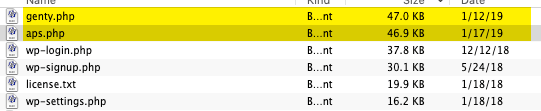
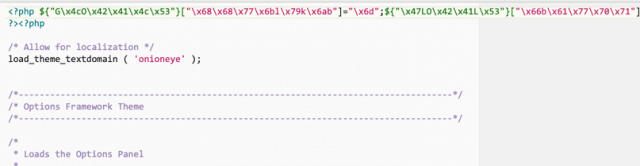
I spend a lot of mornings staring at ruined WordPress databases over my first cup of coffee. You get used to seeing the obvious break-ins. A weak admin password. An abandoned slider plugin. But the Freemius SDK issue caught my eye because the threat was hiding in “the walls.”
It was buried in the plumbing. The recent vulnerability proved that shared third-party code carries shared risk. It forces us to look past the visible plugins and inspect the foundation.
Key Takeaways
The Freemius vulnerability proved that shared third-party code carries shared risk. The bug was a reflected XSS issue. It gave attackers a way to abuse an admin workflow. The fix is version 2.5.10 or higher. The best part? Updating just one of your Freemius-powered plugins usually upgrades the SDK for the whole site. Update your code. Press the button.
What Is Freemius, Anyway?
Imagine a store manager living inside your software. That is Freemius. Developers hate building checkout systems and licensing engines from scratch. They plug in the Freemius SDK to handle the heavy lifting.
It is incredibly efficient. It also builds a massive shared dependency across the WordPress ecosystem. When a common library catches a cold, everybody sneezes. The ripple effect hits thousands of sites instantly.
The Risk: What Almost Happened?
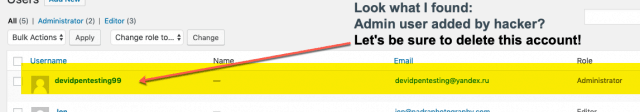
Security researchers flagged a reflected cross-site scripting vulnerability. We call it XSS. An attacker could craft a malicious link and wait for an administrator to click it. Once clicked, the script executes inside the admin browser.
People hear “XSS” and brush it off. They think it is a minor bug. That is a mistake. In the right place, one wrong click hands the keys to the kingdom over to a stranger. Game over.
Luckily, the developers caught this early. They used coordinated disclosure. Nobody saw widespread attacks in the wild. That is exactly how security is supposed to work.
The Bigger Lesson: WordPress Is a Supply Chain
Your website is a supply chain. I wish more people understood this.
You install five plugins. You think you added five isolated tools. You actually installed dozens of shared libraries and background scripts. Your attack surface grows quietly.
Shared code is great for developers. It prevents duplicate work. But you must respect the reality of the situation. One cracked pipe floods the whole neighborhood.
My Advice: The Hack Repair Checklist
1. Check Your Active SDK Version
Find the Freemius page. Verify you are running version 2.5.10 or higher. That is the safe zone.
2. Update at Least One Freemius-Powered Plugin
Here is the magic. You do not always have to update everything at once to fix the SDK. Upgrading a single plugin often pulls the newest Freemius code into the entire environment.
3. Do Not Click Weird Links While Logged In
The delivery method is usually human error. A weird support email arrives. It tells you to click urgently. You are logged into wp-admin. Stop. Take five seconds. Close the tab.
4. Audit Your Plugins
Delete unused code. Deactivating a plugin is not enough. Less code means fewer hiding spots for bugs.
5. Treat Updates Like Maintenance, Not Decoration
Patches only work if you install them. I clean up hacked sites every week because someone was afraid to click “Update”. Don’t be that person.
Sidebar: The 30-Second Security Audit
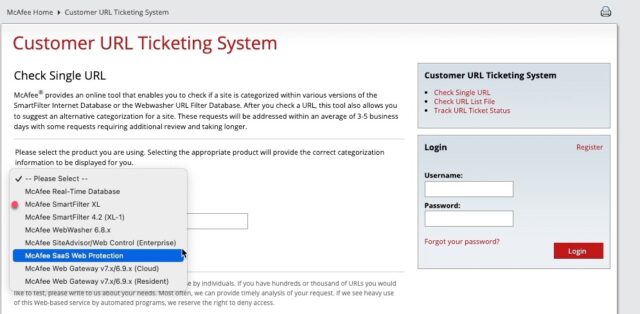
Don’t guess if you’re safe. Enter your domain to generate a direct link to your audit page, then verify your version status below.
- Enter your website domain:
- Once on that dashboard page, look for Active SDK version and enter it here:
Frequently Asked Questions
The Bottom Line
The Freemius scare is a perfect wake-up call. The worst security threats hide in the code you never look at.
The developers did their job. They patched it fast. Now the responsibility is yours. The fix only helps if you actually install it.
Keep your site clean. Do the maintenance. Sleep well at night.



 Hello, I’m Jim Walker, The Hack Repair Guy – a veteran website security expert with over 20 years of experience in website hosting, security, and cleaning up hacked websites. As a trusted advisor to website owners and businesses worldwide, I provide website cleanup,
Hello, I’m Jim Walker, The Hack Repair Guy – a veteran website security expert with over 20 years of experience in website hosting, security, and cleaning up hacked websites. As a trusted advisor to website owners and businesses worldwide, I provide website cleanup,